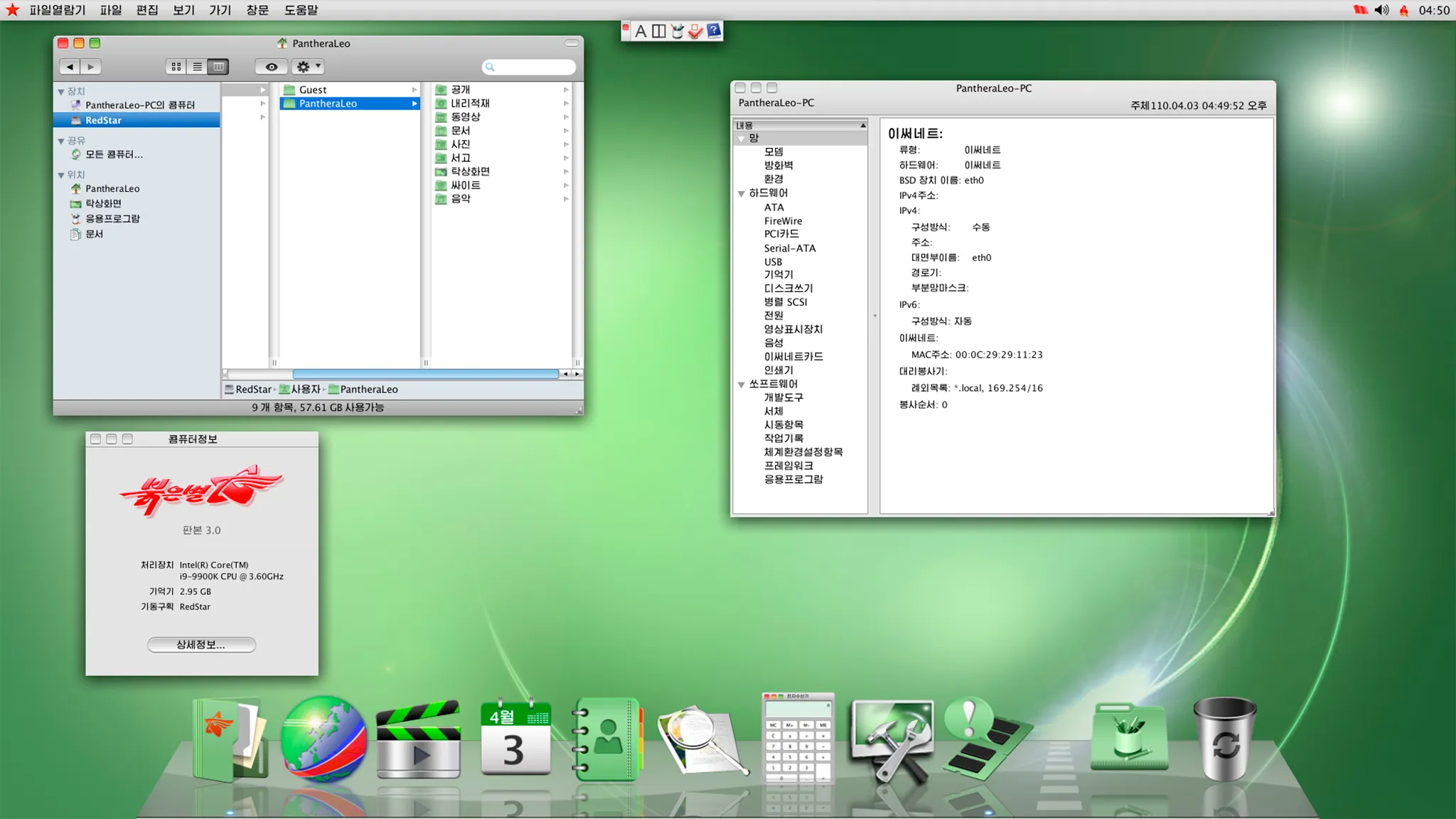
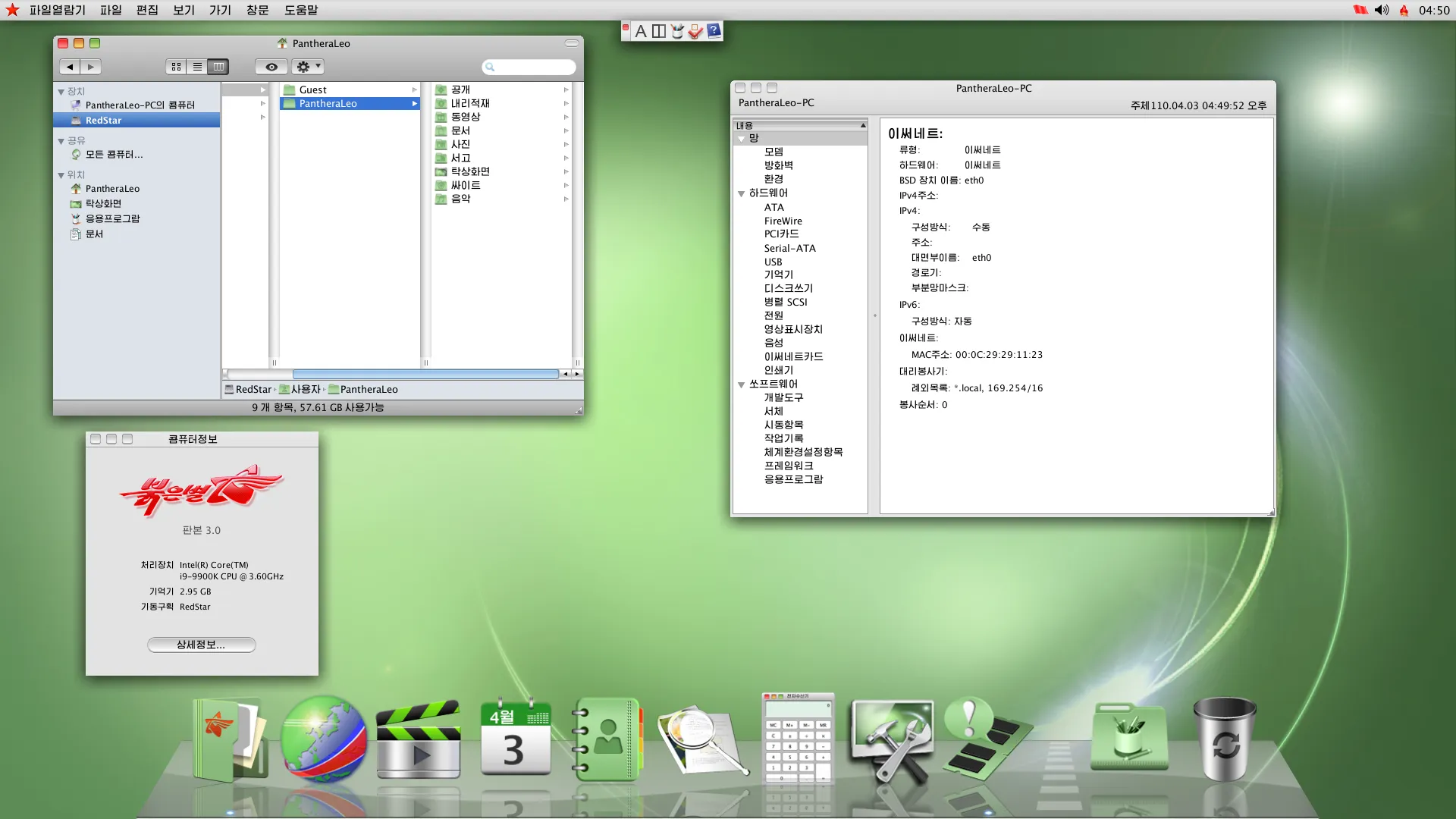
Red Star OS: The North Korea Operating System
North Korea is a country known for its secrecy and strict control over information. One of the technological tools that the North Korean government uses to maintain this control is Red Star OS, an internally developed operating system. This software is emblematic of North Korea’s approach to technology and security, reflecting the country’s philosophy in every aspect of its design and functionality.
Origins and Development
Red Star OS was first introduced in the early 2000s, with the aim of replacing foreign operating systems such as Microsoft Windows, which were widespread in North Korea. The project is part of the juche philosophy, a central principle of North Korean politics that emphasizes self-sufficiency and national independence in all sectors, including technology.

Main Features
Red Star OS is based on Linux, a choice that offers great flexibility and a wide range of development tools. However, the Red Star OS user interface has been strongly modified to resemble Apple macOS. This seemingly unusual design may have been chosen to make the operating system more attractive and familiar to users.
- Control and Censorship: One of the most remarkable features of Red Star OS is its watermarking system. This system inserts unique signs in files to monitor their distribution. Each file created or modified on Red Star OS contains a watermark that identifies the user and device, allowing the government to trace the origin and distribution of files in case of suspicious activity.
- Kwangmyong: North Korea does not allow its citizens free access to global internet. Instead, he developed an internal network called Kwangmyong, which provides access to a limited selection of websites and resources approved by the government. Red Star OS is optimized to work with Kwangmyong, ensuring that users can only access content controlled and approved by authorities.
- Integrated Software: Red Star OS comes with a preinstalled software suite, which includes productivity programs, web browsing (limited to Kwangmyong), and multimedia. Each program has been carefully examined and modified to ensure that it cannot be used to access unauthorized content. For example, the web browser included in the operating system is configured to prevent access to external websites at Kwangmyong.
- System protection: The operating system is equipped with numerous security measures to prevent unauthorized changes. Users do not have access to administrator privileges, which means they cannot install unauthorized software or make significant changes to the operating system. This restriction is designed to prevent the use of software that could bypass censorship and control measures.
Implications for Security and Privacy
Red Star OS uses various implications for security and privacy. On the one hand, the operating system is designed to protect the North Korean government from external threats, such as cyber attacks or the dissemination of unauthorized information. However, at the same time, it strongly limits the freedom of users.
Integrated censorship and continuous monitoring of activities are a significant violation of individual privacy. Each action performed on a computer with Red Star OS can be tracked and monitored by the authorities, making it impossible for users to freely express their views or access unapproved information.
Comparison with Other Operating Systems
Compared to Western operating systems such as Windows, macOS and various Linux distributions, Red Star OS has an unprecedented level of control. While these other operating systems offer users a wide freedom to install software, access the internet and customize their work environment, Red Star OS is designed to prevent all this.
The close integration with Kwangmyong and strict restrictions on administrator privileges make Red Star OS unique in the field of operating systems. In many ways, it is the opposite of the principles of freedom and flexibility that characterize open source operating systems such as Linux.
Final considerations
Red Star OS is a flashing example of how technology can be used to maintain control over a population. Although North Korea presents it as a symbol of technological independence, its features clearly highlight the objective of surveillance and censorship.
For those interested in cybersecurity and freedom of information, Red Star OS is a fascinating and worrying case at the same time. It shows how an operating system can be transformed into a state control tool, severely limiting user freedom and their ability to access uncensored information.